The Ultimate Guide for Engineering Colleges & Universities in India
India is racing toward a digital-first economy-but who will defend it? With over 1.5 million cybersecurity roles expected to remain unfilled by 2025, the answer must begin inside engineering colleges. A dedicated Cybersecurity Lab Setup for Colleges is no longer a luxury-it is a strategic necessity that bridges the dangerous gap between classroom theory and real-world threat response.
This comprehensive guide covers everything from planning a Cyber Security Lab for Engineering Colleges to selecting the right Cybersecurity Lab Equipment List, building an Ethical Hacking Lab, designing a Cybersecurity Center of Excellence, and delivering Hands-On Cybersecurity Lab Training. Whether you are a department head, a lab coordinator, or a university CTO, you will find actionable, India-specific insights here.
Why India Urgently Needs Cybersecurity Labs in Colleges
Before diving into lab design, let us understand the scale of the opportunity-and the crisis-that makes cybersecurity infrastructure in colleges critical today.
| Metric | Value | Context |
| Indian Cybersecurity Market (2024) | ₹21,000+ Crore | Growing at 18% CAGR |
| Cybersecurity Job Openings in India | 1.5 Million+ | Unfilled positions by 2025 |
| Average Ethical Hacker Salary | ₹6–18 LPA | Entry to senior level |
| Avg. Cost of Data Breach in India | $2.18 Million | IBM Security Report 2023 |
| Colleges with Dedicated Cyber Labs | <5% | Huge infrastructure gap |
These numbers tell a clear story: India has a massive talent demand and an equally massive infrastructure gap. Colleges that invest in a proper Cybersecurity Lab Setup in India today will dominate placement records and industry partnerships for the next decade.
1. Cyber Security Lab for Engineering Colleges-Core Concepts
A Cyber Security Lab for Engineering Colleges is more than a room full of computers. It is a controlled, isolated environment where students can simulate attacks, study malware, practice incident response, and develop the intuition that only hands-on experience can build.
What Makes a Great Cybersecurity Lab?
- Air-gapped or VLAN-isolated network to prevent real-world exposure
- Diverse OS environments-Windows Server, Kali Linux, Ubuntu, macOS
- Virtualization infrastructure for spinning up multiple attack/defense scenarios
- Real hardware for network security experiments (routers, switches, firewalls)
- Threat intelligence feeds and up-to-date vulnerability databases
- CTF (Capture the Flag) platforms for gamified, competitive learning
- Industry-standard tools mirroring actual SOC (Security Operations Center) environments
| 💡 Key Insight Labs aligned with certifications like CEH, OSCP, CompTIA Security+, and CISSP produce graduates who skip entry-level and land mid-level roles directly-commanding 40–60% higher starting salaries. |
Learning Outcomes a Cyber Lab Must Deliver
- Penetration testing and vulnerability assessment workflows
- Malware analysis and reverse engineering basics
- Incident response and digital forensics procedures
- Secure code review and application security testing
- Network traffic analysis and anomaly detection
- Cloud security and containerization best practices
2. Cybersecurity Lab Setup in India-Planning & Compliance
Setting up a Cybersecurity Lab in India requires navigating technical, regulatory, and budgetary considerations unique to the Indian higher education landscape.
Regulatory & Policy Alignment
- Align with AICTE’s Model Curriculum for B.Tech Cybersecurity programs
- Follow National Cyber Security Policy 2013 guidelines for institutional labs
- Comply with the IT Act 2000 and its amendments for ethical lab usage
- Consider NASSCOM’s FutureSkills Prime framework for curriculum benchmarking
- Explore DSCI (Data Security Council of India) accreditation for credibility
Budget Planning for Indian Colleges
A well-structured Cybersecurity Lab Setup in India can range from ₹15 Lakhs (basic, 20-seat lab) to ₹2 Crore+ (advanced Center of Excellence). Key budget breakdowns:
- Hardware infrastructure: 35–45% of total budget
- Networking equipment: 20–25% of total budget
- Software licenses & platforms: 15–20% of total budget
- Furniture, power, UPS, cooling: 10–15% of total budget
- Annual maintenance & updates: 10–15% recurring per year
| 💡 Funding Tip Apply for grants under DST (Department of Science and Technology), AICTE MODROBS scheme, and CSR funding from Indian IT companies like Infosys, TCS, and Wipro-many offer lab sponsorships specifically for cybersecurity. |
3. Ethical Hacking Lab Setup for Colleges-Legal, Safe & Effective
An Ethical Hacking Lab Setup for Colleges is the most exciting-and most carefully governed-component of a cybersecurity program. Students must learn to think like attackers while operating within strict legal and ethical boundaries.
Legal Framework for Ethical Hacking Labs
- All attack activities must occur exclusively within isolated lab environments
- Students must sign an acceptable use policy before gaining lab access
- Instructors must hold valid certifications (CEH, OSCP) or equivalent experience
- Lab activities should not involve scanning or probing any external IP address
- All lab exercises must have documented scope, similar to a penetration test SOW
Core Modules for an Ethical Hacking Lab
- Reconnaissance: OSINT tools, Maltego, theHarvester, Shodan (sandboxed)
- Scanning & Enumeration: Nmap, Nessus, OpenVAS vulnerability scanning
- Exploitation: Metasploit Framework against intentionally vulnerable VMs
- Post-Exploitation: Meterpreter, privilege escalation, lateral movement
- Web Application Hacking: DVWA, bWAPP, OWASP WebGoat, Burp Suite
- Password Attacks: Hashcat, John the Ripper on offline hash databases
- Wireless Attacks: WPA2 cracking labs with dedicated hardware adapters
- Social Engineering Simulation: Phishing awareness and defense training
Recommended Vulnerable-by-Design Platforms
- Metasploitable 2/3-Intentionally vulnerable Linux VMs
- DVWA (Damn Vulnerable Web App)-Web application pentesting target
- VulnHub-Hundreds of downloadable challenge VMs
- TryHackMe & HackTheBox-Guided and competitive learning platforms
- OWASP WebGoat-Secure coding practice environment
4. Cybersecurity Training Lab for Universities-Curriculum Architecture
A Cybersecurity Training Lab for Universities must serve multiple stakeholders: undergraduate students, postgraduate researchers, faculty upskilling, and industry training partnerships. The architecture must be modular and scalable.
Tiered Lab Architecture
Tier 1-Foundational Lab (Year 1–2 Students)
- Networking fundamentals with Cisco Packet Tracer and GNS3
- Operating system security hardening (Windows & Linux)
- Basic cryptography implementation labs
- Introduction to OWASP Top 10 vulnerabilities
Tier 2-Intermediate Lab (Year 2–3 Students)
- Penetration testing methodology and practice
- Network traffic analysis with Wireshark
- Vulnerability assessment using Nessus / OpenVAS
- Digital forensics with Autopsy and Sleuth Kit
Tier 3-Advanced Lab (Final Year & PG Students)
- Advanced persistent threat (APT) simulation
- Malware reverse engineering with Ghidra and IDA Free
- Red team vs. Blue team exercises
- Cloud security and DevSecOps pipeline security
- Industrial Control System (ICS/SCADA) security simulation
| 💡 Pro Tip for Universities Partner with platforms like EC-Council Academia, Offensive Security Academic Access Program, or SANS Cyber Academy to get discounted access to world-class curriculum aligned with your lab infrastructure. |
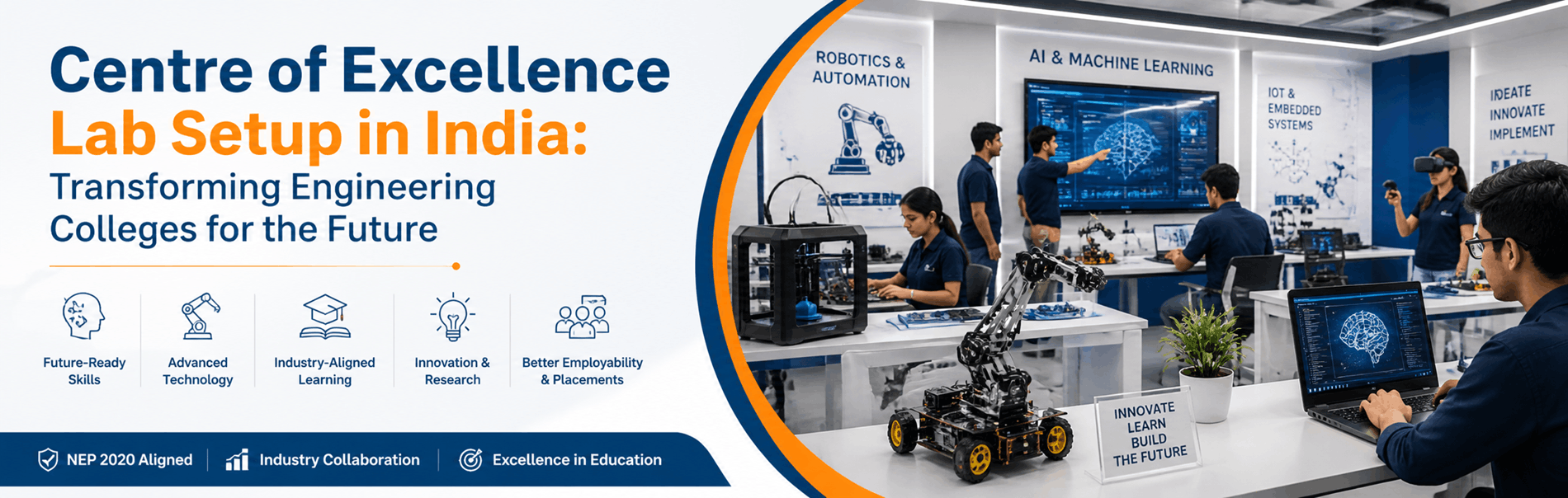
5. Cyber Security Center of Excellence (CoE)-The Gold Standard
A Cyber Security Center of Excellence Lab represents the pinnacle of institutional commitment to cybersecurity education and research. CoEs go beyond teaching to become innovation hubs, research centers, and industry-collaboration nodes.
What Distinguishes a CoE from a Regular Lab?
- 24×7 Security Operations Center (SOC) simulation environment
- Dedicated research cluster for vulnerability research and publication
- Industry collaboration cells for live project work with MNC partners
- Bug bounty program facilitation and responsible disclosure training
- Incident response playbook development and table-top exercise facilities
- Threat intelligence platform (TIP) with live feeds (VirusTotal, AlienVault OTX)
- National and international CTF team development infrastructure
CoE Infrastructure Components
- SIEM Platform: IBM QRadar, Splunk Enterprise, or open-source ELK Stack
- Threat Intelligence: MISP (Malware Information Sharing Platform)
- Deception Technology: HoneyPot cluster (Cowrie, Dionaea, Conpot)
- Malware Analysis Sandbox: Cuckoo Sandbox or Any.Run private deployment
- Forensics Workstation: FTK, EnCase, Magnet AXIOM (licensed)
- Reverse Engineering Lab: Dedicated high-RAM workstations for malware RE
CoE Governance Model
- Industry Advisory Board with representation from CERT-In, DSCI, and IT majors
- Quarterly research symposiums and vulnerability disclosure events
- MoU partnerships with state police cyber cells for real-case study access
- Annual cybersecurity summit hosted by the CoE to attract national attention
6. Network Security Lab Setup for Colleges
A dedicated Network Security Lab Setup for Colleges focuses on the infrastructure layer-where most real-world attacks begin and where defenders must build their strongest capabilities.
Physical Network Lab Topology
- Core Layer: Layer-3 managed switches forming the backbone
- Distribution Layer: Routers with access control lists and routing protocols
- Access Layer: Student-facing managed switches with port security
- DMZ Zone: Simulated internet-facing servers for attack/defense scenarios
- IDS/IPS Segment: Inline Snort/Suricata nodes for real-time detection labs
- Wireless Zone: Dedicated AP cluster for Wi-Fi security testing
Recommended Networking Equipment
- Cisco Catalyst / Juniper EX Series managed switches
- pfSense or Fortinet FortiGate firewall appliances
- Raspberry Pi nodes for IoT security simulation
- Software-Defined Networking (SDN) controller (OpenDaylight / ONOS)
- Network packet broker for traffic mirroring and analysis
Key Network Security Lab Experiments
- ARP spoofing and man-in-the-middle (MITM) attack simulation
- VLAN hopping and inter-VLAN routing attacks
- DDoS simulation and mitigation using rate limiting
- BGP hijacking awareness lab in a controlled GNS3 environment
- SSL/TLS stripping and certificate pinning bypass labs
- Firewall rule bypass and evasion technique studies
7. Cybersecurity Lab Equipment List-Complete Reference
Below is a comprehensive Cybersecurity Lab Equipment List for a 30-seat lab serving undergraduate and postgraduate students, covering hardware, software, and platform requirements.
| Category | Equipment / Tools | Purpose |
| Hardware | High-performance workstations (16+ GB RAM) | Running VMs, simulations, packet analysis |
| Networking | Managed switches, routers, firewalls | Building real network topologies |
| Servers | Rack-mount servers, NAS storage | Hosting lab environments & data |
| Wireless | Access Points, wireless adapters | Wi-Fi security testing & WPA cracking labs |
| IDS/IPS | Snort, Suricata hardware nodes | Intrusion detection & prevention training |
| Virtualization | VMware / Proxmox / VirtualBox | Multi-OS attack/defense environments |
| Tools | Kali Linux, Metasploit, Wireshark, Burp Suite | Penetration testing & vulnerability research |
| Capture the Flag | CTF platforms (PicoCTF, HackTheBox) | Gamified skill building |
| Cloud Lab | AWS/Azure edu accounts | Cloud security & DevSecOps training |
| Safety | Air-gapped network, VLAN isolation | Preventing lab traffic from reaching production |
Minimum Workstation Specifications Per Seat
- Processor: Intel Core i7 12th Gen or AMD Ryzen 7 5800X (8 cores)
- RAM: 32 GB DDR4 (minimum 16 GB; 64 GB for advanced labs)
- Storage: 1 TB NVMe SSD + 2 TB HDD for VM and log storage
- GPU: NVIDIA GTX 1660 or better (required for GPU-accelerated password cracking)
- Network: Dual NIC-one for lab network, one for management VLAN
- OS: Dual-boot Ubuntu 22.04 LTS + Windows 11 Pro
8. Hands-On Cybersecurity Lab Training-Pedagogy & Delivery
Technology alone cannot create cybersecurity professionals. Hands-On Cybersecurity Lab Training requires a carefully designed pedagogical framework that builds intuition, not just technical skills.
The 70-20-10 Learning Model for Cyber Labs
- 70% Hands-On Practice: Students spend the majority of time actively doing-exploiting, defending, and analyzing in the lab
- 20% Collaborative Learning: Red team vs. blue team exercises, peer code review, and group CTF competitions
- 10% Formal Instruction: Lectures, case studies, and industry expert sessions providing conceptual frameworks
Assessment Framework for Lab Training
- Practical exams: Students must demonstrate live exploitation and defense in timed scenarios
- CTF competitions: Weekly internal competitions tracked on a department leaderboard
- Lab reports: Detailed write-ups of each experiment following a professional pentest report format
- Portfolio development: GitHub-hosted security research portfolio for placement interviews
- Capstone project: End-to-end security assessment of a simulated enterprise environment
Industry Certification Alignment
- CompTIA Security+-Foundation for all students in Year 2
- CEH (Certified Ethical Hacker)-Advanced track for Year 3 and final year students
- OSCP (Offensive Security Certified Professional)-Elite track for top performers
- AWS/Azure Security Specialty-Cloud track aligned with Tier 3 labs
- CHFI (Computer Hacking Forensic Investigator)-Forensics specialization track
| 💡 Placement Impact Colleges that run structured, certification-aligned Hands-On Cybersecurity Lab Training report 3–5x higher placement rates in cybersecurity roles compared to those with only theory-based curricula. Average package for CEH+OSCP certified graduates in India: ₹8–15 LPA. |
9. Cybersecurity Lab for Students-Student-Centric Design
The best Cybersecurity Lab for Students is one that students actually want to use-not just during class hours, but in their free time. Design for student engagement, self-directed learning, and community building.
Designing for Student Engagement
- 24×7 access for registered students with multi-factor authentication
- Student-managed CTF team with college branding on national platforms
- Cyber Club integration-monthly workshops, speaker series, bug bounty discussions
- Self-service VM provisioning portal so students can spin up their own environments
- Leaderboard and gamification elements to reward consistent lab engagement
- Dedicated research pods for final year project and thesis work
Student Safety & Privacy in Lab Environments
- All student activity logged and monitored-students are informed of this
- Strict no-tolerance policy for attempting to escape lab network boundaries
- Regular faculty review of lab usage logs for safety compliance
- Clear escalation path for reporting discovered real-world vulnerabilities responsibly
Building a Cybersecurity Community on Campus
- OWASP Student Chapter-globally recognized, free to start
- Null Chapter-India-specific open security community with strong industry ties
- Annual college-level hackathon with cybersecurity tracks
- Alumni mentorship program connecting current students with working security professionals
10. Implementation Roadmap-From Planning to First Lab Session
Use this phased roadmap to guide your Cybersecurity Lab Setup from initial planning to full operational capability.
Phase 1: Foundation (Months 1–3)
- Conduct stakeholder needs assessment and define learning objectives
- Secure budget approval and identify funding sources (AICTE, DST, CSR)
- Finalize lab design and layout with IT infrastructure team
- Procure core hardware: workstations, servers, networking equipment
- Install base networking infrastructure and VLAN isolation
Phase 2: Core Setup (Months 4–6)
- Deploy virtualization platform and base VM library
- Configure SIEM, IDS/IPS, and monitoring infrastructure
- Install and license security tools (Kali, Metasploit, Nessus, Wireshark)
- Set up CTF platform and first set of challenges
- Conduct faculty training program on lab delivery
Phase 3: Launch & Operate (Months 7–12)
- Pilot with a cohort of 30–40 advanced students
- Gather feedback and iterate on lab design and content
- Establish industry partnerships and guest lecture series
- Launch formal certification preparation tracks
- Host first internal CTF competition as a public launch event
Phase 4: Scale & Excellence (Year 2+)
- Expand to Center of Excellence with research mandate
- Onboard industry partners for live project collaboration
- Begin publishing vulnerability research and security advisories
- Apply for national-level recognition (NASSCOM, DSCI, CERT-In tie-ups)
Frequently Asked Questions
Q1: What is the minimum space required for a cybersecurity lab?
A functional 20–30 seat cybersecurity lab requires approximately 800–1,200 square feet. This accommodates workstations, networking equipment racks, a server room enclosure, and a projection area. Advanced CoE-level labs typically require 2,000–4,000 sq ft to accommodate multiple zones.
Q2: Can a cybersecurity lab be built on an open-source budget?
Yes. Using open-source tools (Kali Linux, Metasploitable, Snort, ELK Stack, OpenVAS) and educational licenses from vendors, a highly capable 20-seat lab can be established for ₹15–25 Lakhs. The primary cost is hardware, not software.
Q3: How do we keep the lab legally compliant?
Maintain a clear acceptable use policy, ensure all attack activities occur only on lab-owned assets, log all student activity, and train faculty on IT Act compliance. Consult your institution’s legal advisor and align with AICTE guidelines for lab usage policies.
Q4: What certifications should faculty hold to run a cybersecurity lab?
At minimum, faculty should hold CEH (Certified Ethical Hacker) and CompTIA Security+. For advanced labs, at least one faculty member with OSCP or CISSP significantly elevates the quality of instruction and industry credibility.
Q5: How do we measure ROI on a cybersecurity lab investment?
Track these KPIs: placement rate in cybersecurity roles, average package of cybersecurity-track graduates, number of certifications earned, research papers published, industry MoUs signed, and national CTF competition rankings. Colleges typically see measurable placement ROI within 2 academic cycles.
| Conclusion: The Time to Build is Now The cyber threat landscape does not wait for curriculum committees. Every semester that passes without a dedicated, hands-on Cybersecurity Lab for Students is a semester of graduates entering a battlefield without training. India’s engineering colleges have a historic opportunity-and a responsibility-to become the pipeline for the nation’s cyber defenders. Whether you are starting with a 20-seat Ethical Hacking Lab or scaling up to a full Cyber Security Center of Excellence, the most important step is the first one. Plan strategically, invest in the right equipment, train your faculty, and put your students at the keyboard. The rest will follow. |